Digital Payment Fraud Prevention: Top 5 US Tactics for Early 2026

In the dynamic landscape of early 2026, where digital transactions have become the lifeblood of commerce, the specter of digital payment fraud looms larger than ever. Businesses, consumers, and financial institutions are constantly battling sophisticated threats that evolve with alarming speed. The United States, a global leader in digital innovation, is at the forefront of this fight, deploying cutting-edge strategies to protect its vast and intricate payment ecosystem. This comprehensive article will explore the top five tactics that US businesses are adopting to bolster their defenses against digital payment fraud, ensuring secure and seamless transactions for all.
The rise of e-commerce, mobile payments, and contactless transactions has undeniably brought unparalleled convenience. However, it has also opened new avenues for fraudsters, making robust digital payment fraud prevention an absolute necessity. The financial implications of fraud are staggering, impacting not only the bottom line through chargebacks and lost goods but also eroding customer trust and damaging brand reputation. Therefore, understanding and implementing effective fraud prevention measures is not just good practice; it’s a critical survival strategy in the digital age.
As we navigate the complexities of digital payment fraud in 2026, it’s clear that a multi-layered approach is essential. No single solution can offer complete protection. Instead, a combination of advanced technologies, proactive strategies, and vigilant monitoring forms the bedrock of a resilient fraud prevention framework. Let’s dive into the core tactics that are shaping the future of secure digital payments in the US.
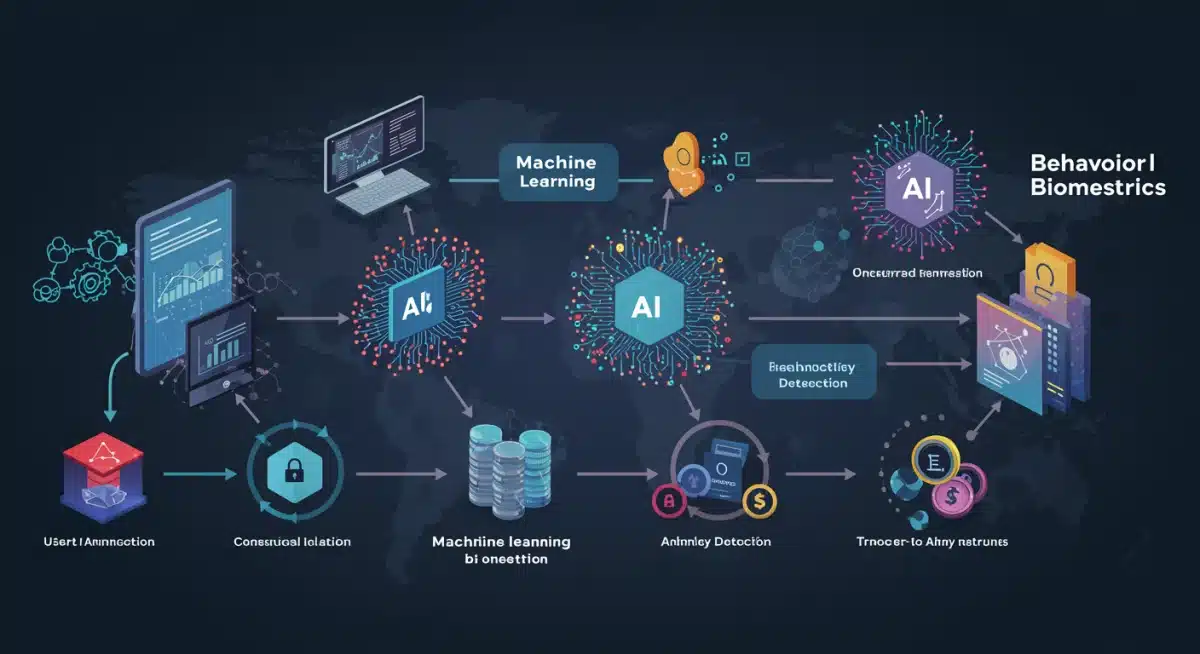
1. Advanced AI and Machine Learning for Real-time Anomaly Detection
The first and arguably most impactful tactic in the fight against digital payment fraud is the sophisticated application of Artificial Intelligence (AI) and Machine Learning (ML). Unlike traditional rule-based systems that can be easily circumvented by cunning fraudsters, AI and ML algorithms possess the ability to learn, adapt, and identify patterns that human analysts might miss. In early 2026, these technologies have reached a new level of maturity, offering real-time anomaly detection capabilities that are revolutionizing fraud prevention.
AI-powered systems analyze vast datasets of transaction histories, customer behaviors, device fingerprints, and network parameters in milliseconds. They can spot deviations from normal behavior, such as unusual purchase amounts, atypical geographic locations for transactions, or rapid successive purchases across different merchants. Machine learning models, particularly deep learning networks, are adept at identifying complex, non-obvious correlations that indicate fraudulent activity. For instance, they can detect synthetic identities by cross-referencing multiple data points that, individually, might seem innocuous but together paint a picture of fraud.
The Evolution of Predictive Analytics
What sets 2026 apart is the enhanced predictive capability of these systems. Rather than merely reacting to suspicious transactions, advanced AI/ML models can now predict the likelihood of fraud before a transaction is even fully authorized. This is achieved through continuous learning from historical fraud data, feedback loops from fraud analysts, and integration with external threat intelligence feeds. The models are constantly refining their understanding of what constitutes fraudulent behavior, making them incredibly difficult for fraudsters to outsmart.
Benefits of Real-time AI/ML Detection:
- Reduced False Positives: While early AI systems sometimes flagged legitimate transactions as fraudulent, today’s advanced models are significantly more accurate, minimizing friction for genuine customers.
- Faster Decision Making: Real-time analysis means transactions can be approved or flagged for review almost instantaneously, maintaining the speed of digital commerce.
- Adaptability: As fraud schemes evolve, AI/ML models can be retrained and updated to recognize new patterns, providing an agile defense.
- Scalability: These systems can handle an immense volume of transactions, making them ideal for large enterprises and growing digital platforms.
For US businesses, investing in robust AI and ML platforms is no longer optional but a strategic imperative to combat digital payment fraud effectively. These tools provide the intelligence needed to stay one step ahead of increasingly sophisticated adversaries.
2. Multi-Factor Authentication (MFA) and Biometrics as Standard Practice
While not a new concept, Multi-Factor Authentication (MFA) has evolved significantly and is now a non-negotiable standard in digital payment fraud prevention for 2026, especially when integrated with advanced biometric technologies. The days of relying solely on passwords are long gone; fraudsters can compromise them through phishing, brute-force attacks, or data breaches. MFA adds crucial layers of security, making it exponentially harder for unauthorized individuals to gain access to accounts or complete fraudulent transactions.
Traditional MFA often involves a combination of something the user knows (password), something the user has (a phone for an SMS code or a hardware token), and something the user is (biometrics). In 2026, the ‘something the user is’ category has become particularly prominent, with biometrics moving beyond simple fingerprint scans to include more sophisticated methods.
The Rise of Behavioral Biometrics
Behavioral biometrics is a game-changer in the fight against digital payment fraud. This technology continuously analyzes unique user behaviors, such as typing cadence, mouse movements, scrolling patterns, device handling, and even the pressure applied to a touchscreen. These subtle, unconscious actions create a unique digital fingerprint for each user. When a deviation from this established behavioral profile is detected during a transaction, it can trigger an additional authentication step or flag the activity as suspicious.
This method offers several advantages:
- Passive and Seamless: Unlike traditional MFA, behavioral biometrics often operates in the background, providing a frictionless user experience while adding a powerful layer of security.
- Continuous Monitoring: It doesn’t just authenticate at login; it continuously verifies the user’s identity throughout the session, detecting account takeover attempts in real-time.
- Hard to Replicate: Behavioral patterns are extremely difficult for fraudsters to mimic, even if they possess stolen credentials.
Beyond behavioral biometrics, US businesses are also heavily investing in advanced physiological biometrics like facial recognition (with liveness detection to prevent spoofing) and voice recognition for high-value transactions. The combination of these methods creates a robust authentication framework that significantly reduces the risk of unauthorized access and fraudulent payments.
3. Enhanced Data Encryption and Tokenization
Data security forms the foundational layer of any effective digital payment fraud prevention strategy. In early 2026, US businesses are prioritizing enhanced data encryption and tokenization techniques to protect sensitive payment information at every stage of the transaction lifecycle. The goal is to render stolen data useless to fraudsters, even if a breach occurs.
End-to-End Encryption
End-to-end encryption ensures that payment data is encrypted from the moment it leaves the customer’s device until it reaches the acquiring bank or payment processor. This means that at no point in transit is the data vulnerable to interception in plain text. Advanced encryption standards, such as quantum-resistant cryptography, are beginning to see adoption, anticipating future threats from quantum computing capabilities that could potentially break current encryption methods.
The Power of Tokenization
Tokenization is another critical defense mechanism. Instead of storing actual primary account numbers (PANs) or credit card details, businesses replace this sensitive information with unique, randomly generated alphanumeric strings called ‘tokens.’ These tokens are useless outside the specific payment ecosystem for which they were generated. If a database containing tokens is breached, the fraudsters gain no valuable payment information, as the original card details are stored securely in a separate, highly protected vault.
For example, when a customer saves their card details for future purchases on an e-commerce site, the actual card number is tokenized. The merchant then stores only the token, which can be used to initiate subsequent transactions without ever re-exposing the actual card number. This significantly reduces the PCI DSS (Payment Card Industry Data Security Standard) compliance burden for merchants and minimizes their risk exposure.
Key Benefits of Encryption and Tokenization:
- Reduced Data Breach Impact: Even if data is stolen, it is encrypted or tokenized, making it unreadable and unusable to unauthorized parties.
- Enhanced Compliance: Helps businesses meet stringent data security regulations and standards.
- Increased Customer Trust: Customers are more likely to transact with businesses that demonstrate a strong commitment to protecting their financial information.
- Minimized Fraud Risk: By making sensitive data inaccessible, these technologies directly thwart various forms of digital payment fraud.
The continuous improvement in encryption algorithms and the widespread adoption of tokenization are pivotal in creating a safer environment for digital payments.
4. Collaborative Fraud Intelligence Sharing and Network Analysis
Fraudsters often operate across multiple platforms, industries, and geographies. Therefore, a siloed approach to digital payment fraud prevention is inherently limited. In early 2026, US businesses are increasingly recognizing the power of collaborative fraud intelligence sharing and network analysis to create a collective defense against organized criminal groups.
Shared Threat Intelligence Platforms
Industry-specific and cross-industry consortiums are emerging, allowing participants to securely share anonymized fraud data, attack patterns, IP blacklists, and other threat intelligence. These platforms leverage advanced analytics to identify common threads and emerging fraud trends that individual organizations might not detect on their own. For instance, if a specific pattern of account takeover attempts is observed by one e-commerce retailer, that intelligence can be rapidly disseminated to others, enabling them to preemptively fortify their defenses.
Financial institutions, payment processors, and merchants are collaborating more closely than ever, understanding that a threat to one is a threat to all. This shared intelligence helps in:
- Identifying Organized Crime Rings: By piecing together data from various sources, it becomes easier to identify and track sophisticated fraud networks.
- Proactive Defense: Businesses can implement new rules or adjust their fraud detection models based on real-time alerts about new attack vectors.
- Faster Response: When a new fraud scheme emerges, the collective intelligence network allows for a much quicker and more coordinated response.
Network Analysis for Fraud Rings
Beyond sharing raw data, advanced network analysis tools are being employed to visualize and understand the connections between suspicious transactions, accounts, and individuals. These tools can map relationships based on shared IP addresses, device IDs, email addresses, phone numbers, or even subtle behavioral linkages. By identifying clusters of fraudulent activity, businesses can uncover entire fraud rings rather than just individual fraudulent transactions.
This approach moves beyond transactional fraud detection to a more holistic understanding of the criminal ecosystem. It allows for the identification of mule accounts, synthetic identities, and organized bot attacks, providing law enforcement and fraud prevention teams with actionable intelligence to disrupt these operations.

5. Robust Identity Verification and Customer Due Diligence (CDD)
The fifth crucial tactic for combating digital payment fraud in early 2026 revolves around robust identity verification and comprehensive Customer Due Diligence (CDD). Preventing fraud often starts at the point of customer onboarding or account creation. By ensuring that genuine customers are who they say they are, businesses can significantly reduce the risk of synthetic identity fraud, account takeovers, and money laundering.
Advanced Identity Verification (IDV)
Traditional IDV methods, such as checking government-issued IDs, are being augmented with sophisticated digital tools. These include:
- AI-Powered Document Verification: Using AI to scan and authenticate identity documents, checking for signs of tampering, holograms, and security features, often combined with facial recognition to match the document holder to a live selfie.
- Digital Footprint Analysis: Verifying identities by analyzing publicly available digital data, such as social media profiles, professional networks, and online presence, to build a more complete picture of the applicant.
- Cross-Referencing with Trusted Data Sources: Integrating with credit bureaus, utility providers, and other reliable databases to confirm address, phone number, and other personal details.
- Liveness Detection: Crucial for biometric verification, ensuring that a live person is present during the authentication process and not a photo, video, or mask.
Continuous Customer Due Diligence (CDD)
CDD is not a one-time event; it’s an ongoing process. Businesses are implementing continuous monitoring of customer accounts for suspicious activity that might indicate an account takeover or a change in risk profile. This includes:
- Transaction Monitoring: As discussed with AI/ML, continuously analyzing transaction patterns for anomalies.
- Behavioral Biometrics: As mentioned earlier, passively verifying the user’s identity throughout their session.
- Periodic Reviews: For high-risk accounts or those with significant activity, periodic re-verification of identity or updated documentation may be required.
The goal of robust IDV and CDD is to create a trusted digital environment where customers can feel confident that their identities are secure and that they are transacting with legitimate entities. This proactive approach significantly reduces the entry points for fraudsters and builds a strong foundation for overall digital payment fraud prevention.
The Future Outlook: Staying Ahead of Digital Payment Fraud
As we look beyond early 2026, the battle against digital payment fraud will undoubtedly intensify. Fraudsters are highly adaptive, constantly seeking new vulnerabilities and refining their techniques. Therefore, the strategies discussed above are not static solutions but rather dynamic frameworks that require continuous evolution and investment.
Emerging technologies like blockchain for immutable transaction records, homomorphic encryption for secure data processing, and further advancements in quantum computing (both as a threat and a potential solution for cryptography) will shape the next generation of fraud prevention tools. The emphasis will remain on creating a seamless yet secure user experience, balancing convenience with impenetrable defenses.
For US businesses, the key to long-term success in combating digital payment fraud lies in fostering a culture of security, investing in cutting-edge technologies, and actively participating in collaborative intelligence networks. It also involves educating customers about common fraud schemes and best practices for online safety, empowering them to be the first line of defense.
The digital economy thrives on trust. By implementing these top five tactics – advanced AI/ML, robust MFA and biometrics, enhanced encryption and tokenization, collaborative intelligence sharing, and stringent identity verification – US businesses can build a resilient defense against digital payment fraud, safeguarding their assets, their customers, and their reputation in an increasingly interconnected world.
The landscape of digital payments is constantly shifting, and with it, the methods employed by those who seek to exploit its vulnerabilities. The proactive and multi-faceted approach outlined here represents the pinnacle of digital payment fraud prevention in early 2026, setting a high standard for security and paving the way for a more secure digital future.





