Fintech Incident Response Planning: 7 Steps for 2026 Cyber Resilience

In the rapidly evolving landscape of digital finance, US fintech companies are at the forefront of innovation, but also increasingly in the crosshairs of sophisticated cyber threats. The year 2026 looms large with predictions of even more advanced and frequent cyberattacks, making a robust Fintech Incident Response plan not just a recommendation, but an absolute necessity. A well-defined incident response strategy can mean the difference between a minor disruption and a catastrophic business failure, safeguarding customer trust, financial assets, and reputation.
The financial sector, by its very nature, handles sensitive data and large sums of money, making it a prime target for malicious actors. Fintechs, with their often-leaner security teams and rapid deployment cycles, can be particularly vulnerable. Regulatory bodies are also tightening their grip, demanding higher standards of cybersecurity and incident preparedness. Non-compliance can lead to hefty fines, legal repercussions, and severe reputational damage. This comprehensive guide will walk US fintechs through a critical 7-step framework for developing and implementing an effective Fintech Incident Response plan, designed to mitigate the impact of cyberattacks and ensure business continuity in the face of adversity.
The Escalating Threat Landscape for US Fintechs
Before diving into the specifics of incident response, it’s crucial to understand the evolving threat landscape. Cybercriminals are becoming more sophisticated, utilizing AI-driven attacks, ransomware-as-a-service, supply chain compromises, and highly targeted phishing campaigns. For US fintechs, this means facing threats that are not only more complex but also more frequent and potentially devastating. The interconnected nature of financial systems means that a breach in one area can have ripple effects across the entire ecosystem. Moreover, the increasing adoption of cloud services, APIs, and third-party integrations, while enabling innovation, also expands the attack surface, creating new vulnerabilities that must be addressed proactively through a strong Fintech Incident Response framework.
Why a Proactive Fintech Incident Response Plan is Indispensable
Many organizations unfortunately view incident response as a reactive measure – something to think about only after a breach has occurred. This is a critical mistake, especially for fintechs. A proactive approach to Fintech Incident Response offers numerous benefits:
- Minimizing Financial Losses: Swift response can limit data exfiltration, service disruption, and fraudulent transactions, directly reducing monetary impact.
- Protecting Reputation and Customer Trust: A well-managed incident demonstrates competence and commitment to security, helping to retain customer loyalty. Conversely, a poorly handled incident can erode trust irrevocably.
- Ensuring Regulatory Compliance: Regulators like the CFPB, SEC, and state-level financial authorities have stringent requirements for incident reporting and data breach notification. A plan ensures these obligations are met.
- Maintaining Business Continuity: By having clear procedures for recovery, fintechs can minimize downtime and resume critical operations quickly.
- Reducing Legal Exposure: Proper incident handling can mitigate potential lawsuits from affected customers or partners.
- Improving Security Posture: Each incident, when properly analyzed, provides valuable lessons that can be used to strengthen overall security defenses.
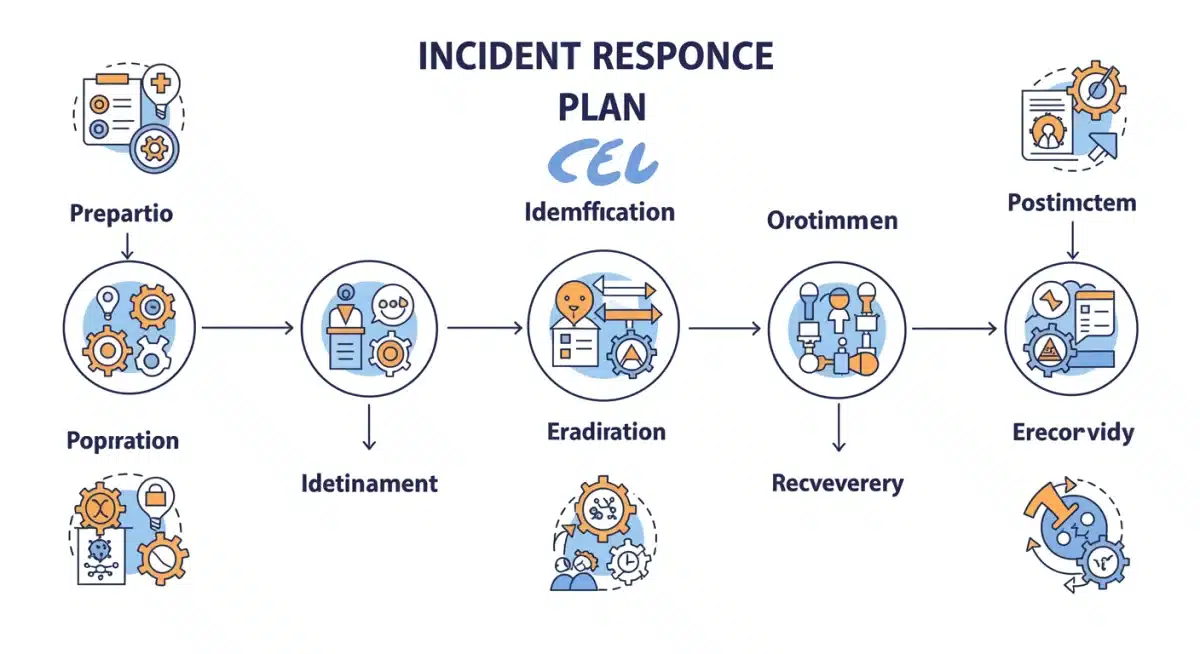
The 7-Step Fintech Incident Response Guide for 2026 Mitigation
Drawing inspiration from industry best practices and frameworks like NIST (National Institute of Standards and Technology), this 7-step guide is tailored to the unique challenges and requirements of US fintechs. Each step is crucial and interconnected, forming a comprehensive strategy for effective Fintech Incident Response.
Step 1: Preparation – Laying the Foundation for Resilience
The first and arguably most important step in Fintech Incident Response is preparation. This isn’t just about having a document; it’s about building a security-aware culture and robust infrastructure before an incident even occurs. Without thorough preparation, subsequent steps will be significantly hampered.
Key Activities in Preparation:
- Develop a Comprehensive Incident Response Policy: This policy should outline the scope, roles, responsibilities, and overall strategy for incident handling. It should be approved by senior management and regularly reviewed.
- Form an Incident Response Team (IRT): Identify and train a dedicated team with diverse skills, including technical experts (security analysts, network engineers, forensic specialists), legal counsel, communications specialists, and senior management representatives. Define clear roles and communication protocols for the IRT.
- Implement Security Controls: This includes firewalls, intrusion detection/prevention systems (IDS/IPS), Security Information and Event Management (SIEM) systems, endpoint detection and response (EDR), multi-factor authentication (MFA), data encryption, and regular vulnerability assessments and penetration testing.
- Establish Robust Logging and Monitoring: Ensure comprehensive logging across all systems and applications. Centralize logs for easier analysis and integrate them with your SIEM for real-time alerting on suspicious activities.
- Create Communication Plans: Define who needs to be informed, when, and how (e.g., internal stakeholders, customers, regulators, law enforcement, media). Prepare pre-approved communication templates for various incident types.
- Develop Playbooks for Common Incidents: Create detailed, step-by-step guides for handling specific types of incidents, such as ransomware, phishing, data breaches, or DDoS attacks.
- Conduct Regular Training and Drills: The IRT and relevant staff must be regularly trained on their roles and responsibilities. Conduct tabletop exercises and simulated cyberattacks to test the plan’s effectiveness and identify weaknesses.
- Secure Backups: Implement a robust, tested backup strategy for all critical data, ensuring backups are immutable, isolated from the network, and regularly verified for integrity and restorability.
- Vendor Risk Management: Assess the cybersecurity posture of all third-party vendors and partners. Ensure their security controls align with your own and that their contracts include incident response clauses.
Step 2: Identification – Detecting and Triage
Once preparation is in place, the next step is to effectively identify and triage potential security incidents. Early detection is paramount in limiting damage. This phase focuses on recognizing an event as an incident and gathering initial information.
Key Activities in Identification:
- Continuous Monitoring: Utilize your SIEM, EDR, and other security tools to continuously monitor network traffic, system logs, user behavior, and security alerts.
- Alert Triage and Analysis: Security analysts must be proficient at triaging alerts, distinguishing between false positives and genuine threats. This involves correlating data from multiple sources.
- Initial Scope Assessment: Once a potential incident is identified, determine its initial scope – what systems are affected? What data might be compromised? Who are the potential victims?
- Documentation of Initial Findings: Begin documenting everything immediately – timestamps, affected systems, observed symptoms, and initial hypotheses. This forms the basis for forensic analysis.
- Incident Classification and Prioritization: Classify the incident based on its type, severity, and potential impact on business operations, customer data, and regulatory compliance. Prioritize incidents based on their potential damage.
- Activate the IRT: Based on the incident’s classification and priority, activate the relevant members of the Incident Response Team.
Step 3: Containment – Stopping the Bleeding
Containment is about preventing the incident from spreading further and causing more damage. This requires swift and decisive action to isolate affected systems and networks, protecting unaffected assets.
Key Activities in Containment:
- Short-Term Containment: Implement immediate measures to stop the spread. This might involve isolating compromised systems, disconnecting networks, blocking malicious IP addresses at the perimeter, or disabling compromised user accounts.
- Long-Term Containment: Develop a strategy to fully isolate and prevent recurrence. This could involve patching vulnerabilities, reconfiguring firewalls, or deploying new security tools.
- Evidence Preservation: While containing the incident, it’s critical to preserve forensic evidence. Create disk images, capture network traffic, and maintain detailed logs without altering the original data.
- Backup and Snapshotting: If possible, take snapshots or backups of affected systems before making significant changes for forensic purposes.
- Communication Updates: Provide initial updates to relevant stakeholders as per the communication plan, without disclosing sensitive details prematurely.
Step 4: Eradication – Eliminating the Threat
Once contained, the next step is to eradicate the root cause of the incident and remove all traces of the attacker. This ensures that the threat is completely neutralized and cannot re-emerge.
Key Activities in Eradication:
- Identify Root Cause: Conduct thorough forensic analysis to determine how the attacker gained access, what vulnerabilities were exploited, and what actions they took.
- Malware Removal: Remove all malicious software from affected systems.
- Vulnerability Patching: Apply all necessary security patches to address the exploited vulnerabilities.
- System Hardening: Implement additional security configurations and controls to harden systems against similar future attacks.
- Credential Reset: Force password resets for all compromised accounts and potentially for all users if the scope of compromise is widespread. Implement strong password policies and MFA.
- Rebuild or Restore: In some cases, it may be necessary to completely rebuild systems from trusted images or restore from clean backups to ensure complete eradication.
Step 5: Recovery – Restoring Operations
With the threat eradicated, the focus shifts to restoring affected systems and services to full operation. This phase aims to minimize downtime and ensure business continuity.
Key Activities in Recovery:
- System Restoration: Restore affected systems and data from clean backups or rebuild them from scratch, ensuring all patches and security configurations are applied.
- Verification and Testing: Thoroughly test all restored systems and applications to ensure they are functioning correctly and that no lingering vulnerabilities or malicious code remain.
- Monitoring for Recurrence: Implement enhanced monitoring during the recovery phase to detect any signs of the attacker attempting to regain access or new threats emerging.
- Gradual Reintroduction: Reintroduce systems and services back into the production environment gradually, monitoring performance and security at each step.
- Communicate Recovery Progress: Keep stakeholders informed about the recovery progress and estimated timelines for full service restoration.

Step 6: Post-Incident Activity – Learning and Improving
The incident isn’t truly over until a thorough post-mortem analysis has been conducted. This critical step ensures that lessons are learned and the organization’s security posture is continuously improved. This is where the true value of a robust Fintech Incident Response process shines.
Key Activities in Post-Incident Activity:
- Lessons Learned Meeting: Conduct a “lessons learned” meeting with all relevant parties. Discuss what happened, how it was handled, what worked well, and what could be improved.
- Incident Report Generation: Create a detailed incident report documenting the entire lifecycle of the incident, including:
- Executive Summary
- Incident Details (type, scope, impact)
- Timeline of events
- Actions taken during each phase
- Root cause analysis
- Financial and reputational impact
- Recommendations for improvement
- Action Item Creation: Based on the lessons learned, create specific, measurable, achievable, relevant, and time-bound (SMART) action items to address identified weaknesses.
- Policy and Procedure Updates: Update incident response policies, playbooks, security controls, and training materials based on the incident findings.
- Regulatory Reporting: Fulfill all mandatory regulatory reporting requirements within the specified timelines. This is a critical aspect for US fintechs operating under various financial regulations.
- Public Disclosure (if necessary): If a data breach occurred, manage public disclosure carefully and transparently, adhering to legal and ethical guidelines.
- Review and Update Vendor Agreements: If a third-party vendor was involved, review and potentially update service level agreements (SLAs) and security clauses.
Step 7: Continuous Improvement – Adapting to New Threats
Cybersecurity is not a static state; it’s a continuous process. The threat landscape is constantly evolving, and so too must your Fintech Incident Response capabilities. This final step emphasizes an ongoing commitment to enhancing security.
Key Activities in Continuous Improvement:
- Regular Review of the IR Plan: Annually, or more frequently if significant changes occur, review and update the entire incident response plan.
- Advanced Threat Intelligence Integration: Continuously monitor threat intelligence feeds relevant to the financial sector and integrate them into your security operations to anticipate new attack vectors.
- Technology Upgrades: Invest in new security technologies and tools as needed to keep pace with evolving threats.
- Ongoing Training and Awareness: Provide continuous cybersecurity training for all employees, not just the IRT, to foster a strong security culture.
- Regular Drills and Simulations: Conduct periodic, unannounced incident response drills and tabletop exercises to test the plan and keep the IRT sharp. Consider involving external parties for fresh perspectives.
- Benchmarking: Compare your incident response capabilities against industry benchmarks and best practices.
- Audit and Compliance Checks: Regularly audit your security controls and processes to ensure compliance with relevant regulations and internal policies.
Regulatory Compliance and Legal Considerations for US Fintechs
For US fintechs, navigating the complex web of regulations is as crucial as technical preparedness. A robust Fintech Incident Response plan must explicitly address compliance requirements. Key regulations and considerations include:
- Gramm-Leach-Bliley Act (GLBA): Requires financial institutions to explain their information-sharing practices to customers and to safeguard sensitive data.
- State Data Breach Notification Laws: Each state has its own requirements regarding when and how to notify individuals and state attorneys general about data breaches. Fintechs must be aware of and comply with laws in all states where their customers reside.
- NIST Cybersecurity Framework: While voluntary, many financial regulators look to NIST standards as a benchmark for cybersecurity best practices.
- Payment Card Industry Data Security Standard (PCI DSS): If your fintech handles credit card data, PCI DSS compliance is mandatory.
- SEC Requirements: The Securities and Exchange Commission has heightened expectations for public companies (and those aspiring to go public) regarding cybersecurity risk management and incident disclosure.
- CFPB Guidelines: The Consumer Financial Protection Bureau provides guidance on protecting consumer financial data.
- Contractual Obligations: Review all contracts with third-party vendors and partners for incident notification and liability clauses.
Legal counsel must be involved early in the incident response process to ensure all actions comply with applicable laws and regulations, particularly regarding data breach notification and evidence handling.
Building a Culture of Security within Your Fintech
Technology and processes are only part of the equation. Human error remains a significant factor in many security incidents. Therefore, fostering a strong culture of security is an integral component of effective Fintech Incident Response.
- Leadership Buy-in: Cybersecurity must be championed by senior leadership, demonstrating its importance through resource allocation and active participation.
- Regular Employee Training: Beyond technical staff, all employees should receive regular training on phishing awareness, secure coding practices, data handling, and reporting suspicious activities.
- Clear Policies and Procedures: Ensure that security policies are well-documented, easily accessible, and understood by all employees.
- Reporting Mechanisms: Establish clear and easy-to-use channels for employees to report potential security concerns without fear of reprisal.
- Security Champions: Identify and empower security champions within different departments to promote best practices and act as a first point of contact for security questions.
The Role of Automation and AI in Fintech Incident Response
As cyberattacks grow in volume and sophistication, manual incident response processes can be overwhelmed. Automation and Artificial Intelligence (AI) are becoming indispensable tools for enhancing Fintech Incident Response capabilities.
- Security Orchestration, Automation, and Response (SOAR): SOAR platforms can automate repetitive tasks, orchestrate workflows across different security tools, and provide automated responses to certain types of incidents, significantly reducing response times.
- AI-driven Threat Detection: AI and machine learning algorithms can analyze vast amounts of data to detect anomalies and identify emerging threats more quickly and accurately than traditional rule-based systems.
- Automated Forensics: Tools leveraging AI can assist in automated log analysis, malware analysis, and even predict potential attack paths.
- Predictive Analytics: AI can help analyze historical incident data to predict future attack patterns and proactively strengthen defenses.
While AI and automation offer powerful advantages, they are not a silver bullet. Human oversight, expertise, and strategic decision-making remain critical, especially in complex incidents. The goal is to augment human capabilities, not replace them.
Conclusion: Fortifying Your Fintech for 2026 and Beyond
The digital financial landscape is a battleground, and for US fintechs, preparedness is the ultimate weapon. A meticulously crafted and regularly practiced Fintech Incident Response plan, following the 7-step guide outlined above, is fundamental to navigating the complex and dangerous cyber threat environment of 2026 and beyond.
By prioritizing preparation, ensuring rapid identification and containment, executing thorough eradication and recovery, and committing to continuous improvement, fintechs can build an unshakeable foundation of cyber resilience. This not only protects the organization’s assets and reputation but also reinforces the trust of customers who rely on these innovative financial services. Invest in your incident response capabilities today; it’s an investment in your fintech’s future stability and success.





